Risk Considerations for Continued Business Operations in Russian Critical Infrastructure Sectors
State of Play, Ukraine Crisis
Special thanks to Bill Moore, who also contributed to this post.
The Bottom Line
While moral or ethical considerations are beyond the typical scope of our advisories, in the current circumstances we'd recommend every company currently operating in Russia strongly weigh them. The following document is meant to outline a state of play for those facing heightened risk as they consider future presence in the region.
It will become increasingly difficult, if not inhospitable, for companies operating in Russian critical infrastructure sectors to rely on western-made software. Expect increased requests from Russian authorities like the Federal Security Service (FSB), for example, to transition from Azure or AWS to Yandex or Mail.ru.
Russian authorities, foremost the FSB, will view western firms operating in critical infrastructure sectors with increasing suspicion. Their guiding assumption will be that U.S. intelligence leverages non-Russian-made software at best for intelligence collection, at worst for prepositioning destructive cyberattacks.
Companies may find themselves, their products, and services becoming pawns in a broader geopolitical contest—particularly as Russian state organizations increasingly publicize attribution of cyberattacks and intrusions that are at odds with the findings of western entities. In these situations, companies may face pressure to join Russia’s information sharing organizations—rough equivalents to U.S. sector-based Information Sharing and Analysis Centers (ISACs)—and corporately endorse their findings.
Business leaders should operate on the assumption that the legal and regulatory environment in Russia is likely to tighten alongside the deteriorating geopolitical dynamic between Russia and the West—and be proactive in tailoring their business operations and managing their elevated risk profiles to reflect that likelihood.
State of Play: Perspectives on Critical Infrastructure in Russia
Much of the cybersecurity industry’s focus in recent days has (rightfully) been on raising awareness and resilience for the operators of U.S. critical infrastructure, considering heightened tensions stemming from Russian aggression toward Ukraine. However, a number of multinationals continue operations in Russia (even amidst increasing U.S. and European Union sanctions pressure). According to a recent survey by the American Chamber of Commerce, U.S. businesses invested $2.2 billion in the Russian economy in 2020 and planned to invest around $1.8 billion more in 2021 – over half this money in Russia’s energy and natural resources sectors (wherein some sanctions carve-outs are in effect). Such businesses should consider the role they play in what Moscow considers critical infrastructure, assess their relationships and attack surface, and create plans to mitigate the risks they will face in the intensifying geopolitical crisis.
Early last month, Russian official Nikolay Murashov, Deputy Director of Russia’s National Coordination Center for Computer Incidents (NKTsKI) noted the following:
“NATO and members of the North Atlantic bloc have dubbed the Russian Federation an aggressor-state, and they are making preparations for serious offensive operations. I’m thus convinced that we simply cannot use technical protection solutions from foreign developers in securing Russia’s critical information infrastructure. Doing so would present a danger, foremost because of their inherent vulnerabilities.”
This sentiment follows years of Kremlin efforts to indigenize Russia’s tech sector and months of pressure on U.S. social media giants to adopt the Kremlin’s content moderation schema. Despite these pushes, Russia remains heavily dependent on western technologies in its public infrastructure and private sectors and could not excise them quickly without incurring significant damage to its economy.
A rough analog to the U.S. Cybersecurity and Infrastructure Security Agency (CISA), NKTsKI was established in late 2018 to detect, analyze, coordinate, and respond to cyber incidents within Russian critical infrastructure. NKTsKI falls under the Russian SB’s Scientific-Technical Center, which is tasked with securing and encrypting government networks. Ironically, sister-organizations within the FSB pose some of the primary cybersecurity threats to critical infrastructure in Ukraine and the United States, judging from industry and government reporting.
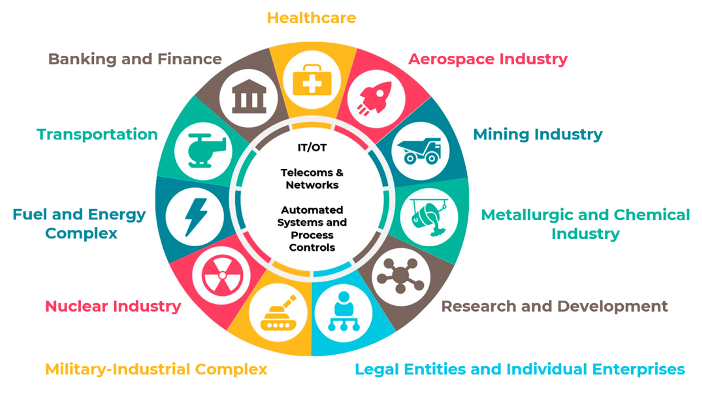
This red-team/blue-team dynamic is more than a mere bureaucratic feature. In the context of the current conflict, creates dueling imperatives for western businesses doing business in Russia—particularly if they operate in the below sectors.
Russian Critical Infrastructure Sectors
Meanwhile, a new crop of Russian sector-level groupings—rough analogs to U.S. ISACs—have recently emerged. Earlier this month, the Ministry of Finance announced the establishment of a cybersecurity operations center designed to not only monitor for and mitigate intrusions, but also issue formal attributions, building on an earlier iteration called “FinCERT.” The Ministry of Energy also announced “EnergyCERT,” a collaborative performing similar functions in the energy sector.
These types of collaborative efforts, however, rely far less upon the goodwill of their participants than ISACs in the United States, and could serve as much to advance Moscow’s geopolitical and propaganda objectives as to exchange legitimate cybersecurity insights. They are part of a broader federal system called GosSOPKA, the State System of Detecting, Preventing, and Eliminating the Consequences of Computer Attacks on Russia’s Information Resources. This system is the culmination of nearly a decade of federal legislation aimed at systematizing and centralizing Moscow’s capacity to defend domestic networks and critical infrastructure. Federal Law No. 187-FZ, which went into effect in 2018, obligates organizations in these sectors to notify authorities—such as the NKTsKI—within a ten-day period of computer incidents; assist in the detection, prevention, and remediation of cyberattacks; and ensure procedures and technical mitigations are in place.
This extensive regulatory and legislative regime already imposed significant burdens on operators in these sectors. During heightened military and cyber activity, these demands are likely to intensify and be driven and shaped by exogenous geopolitical factors. Western businesses operating in the Russian market writ large need to brace for potentially drastic economic measures by the Kremlin, of the kind not seen since the early 1990s—when major assets were gradually nationalized (then under the guise of “privatization”). Responding to the influx of U.S. and EU sanctions, former Russian President Dmitriy Medvedev recently went so far as to advocate for state seizure of Western assets, calling for “the nationalization of property belonging to entities registered in unfriendly jurisdictions.”
Recommendations
Operating in Russian markets has always carried heightened risk for western businesses. However, amidst an intensifying military conflict, executives must consider the likelihood that Moscow will crack down on or exploit any foreign elements remaining within its domestic cybersecurity landscape, using the full weight of state and private stakeholder organizations. This dynamic is already posing rapid and consequential decisions for corporate leaders.[1] Below are some steps companies in this position should take:
Develop contingency plans for an eventual voluntary—if not compulsory—shift to indigenous Russian componentry, operating and control systems, or security software.
Conduct scenario-based planning for a partial (or complete) exit from the Russian market, should events dictate.
Map out your Russian networks and infrastructure, including creating an inventory of critical systems and data in-country.
Evaluate the risks of reliance on indigenously produced Russian products in their technical stack—particularly for any data or IP stored or passed through them.
Update risk registers to reflect the increased espionage and surveillance threats they might pose.
Isolate and sequester Russia-based networks and data holdings from broader corporate network architecture.
Enhance identity verification, operate on principle of least privilege, and dedicate additional threat-monitoring resources to Russia-based systems and networks.
Consider the security impact of Russian WAN and VPN links, especially those that are not fully encrypted.
Consider security measures that provide some protection in case of loss-of-control, such as encrypted volumes that must be mounted remotely with off-system keying material.
Revise risk registers to include potential impacts to business operations, as well as downstream effects to customers.
Ensure governmental affairs and global communications shops remain in close coordination to enforce both accuracy and sensitivity in messaging.