Shields Up v2: Defending Against Russian Information Operations
Tags: Shields Up, Ukraine Crisis
As the Russian invasion of Ukraine continues, cyber-enabled information operations will not be confined to nation-state entities. Businesses may also be targeted by cyber actors, if they are perceived as aligned with U.S. or western interests.
State of Play: Russia’s Reliance on Propaganda
Russian efforts in the information space are not only limited to conventional warfare and cyber operations, but also include cyber-enabled information operations that yield significant technical and psychological effects. Russian military, intelligence, and political leaders are adept at manipulating the information environment to advance Kremlin objectives. State-backed outlets in traditional and social media are key tools in their arsenal to shape audience perception. These operations are low-cost and provide an asymmetric advantage against adversaries whose societies and governance rely on trust and transparency to operate effectively.
Notably, Moscow wields its propaganda machine to justify impending military actions and garner support. For months preceding physical military action in Ukraine, Russian state-backed outlets coordinated a narrative of Ukraine as a neo-Nazi state – waging a genocide against ethnic Russians in the Donbas region. Immediately prior to Russia’s invasion of Ukraine, U.S. State Department spokesperson Ned Price detailed the uptick of untrue, “reports of unmarked mass graves of civilians allegedly killed by Ukrainian Forces” and claims that, “the United States or Ukraine are developing biological or chemical weapons…for use in the Russian-controlled territories.” Senior U.S. officials attempted to neutralize these tactics by exposing and preempting them: in an unprecedented response, U.S. intelligence agencies publicly revealed an elaborate Russian security service plot to produce propaganda videos of a staged Ukrainian attack as a pretext for invasion.
Risk Landscape: Information Operations and Corporate Risk
With the on-going deployment of information operations from the Russian government and military, business executives should prepare to identify and respond to threats ranging from overt propaganda to covert information operations. Given the public outcry in response to events unfolding in Ukraine and corporate banning of Kremlin-backed media outlets by companies including Meta, YouTube, Netflix, and DirecTV, overt Russian state-backed behaviors in the information space are, at this point, unlikely to elicit support or cause significant direct reputational harm. Though some overt messaging channels are still sharing state-backed content from organizations like the Strategic Cultural Foundation, information covertly aligned with Russian state-backed actors presents the largest threat to organizations Russia perceives as adversarial.
Covert information operations – where the audience is unaware of the content origination or author affiliation – have the potential to advance Moscow’s objectives without explicit attribution. This deniability enables strategic narratives to be laundered via seemingly legitimate outlets. Facebook’s public security announcement about the threat actor group, Ghostwriter, illustrates the utility of these tactics in the current Russia-Ukraine information space. The operation leveraged compromised, legitimate social media accounts to disseminate disinformation with the intent to distort public perception of the conflict; one video distributed depicted a Ukrainian surrender. In response to the threat of disinformation, corporate monitoring initiatives should focus on identifying efforts that call into question the availability of goods and services or alleging service outages, with clear remediation statements at-the-ready from global communications shops.
An uptick in Russian-state backed cyber attacks, including information operations, is expected in response to U.S.-levied sanctions and the subsequent increases in market competition. Targeted propaganda efforts may cause reputational damage by directly discrediting an organization or pushing a market segment toward a Russian or allied competitor. For example, COVID-19 vaccine manufacturers were targeted by both covert and overt Russian information operations attempting to sow doubt and promote the Russian alternative, Sputnik V. As Russian state-backed sectors, organizations, and products struggle in response to U.S. sanctions, western organizations in competitor sectors could similarly be the targets of Russian disinformation campaigns.
More advanced attacks may employ hybrid ‘hack and leak’ operations, wherein sensitive information obtained via breached infrastructure is shared (and often mis-contextualized) to maximize cyber and reputational damages. This approach was demonstrated during the 2016 presidential election, when Russian intelligence officers spear-phished the Democratic campaign, accessed internal documentation, and leaked it publicly under the names ‘DCLeaks’ and ‘Guccifer 2.0’. More recently, hack and leak and doxxing techniques have been used against Russian military targets, which may raise the likelihood Russia will utilize equivalent techniques in response. Organizations with particularly sensitive private information and objectives in conflict with Russian strategic interests could be subject to these attacks.
In the worst case, an information operation that successfully inflames online discourse could move offline and manifest as real-world protests or physical attacks on an organization’s assets. Overt Russian leveraging of disinformation campaigns to trigger offline responses was also demonstrated during the 2016 election. Facebook, Twitter, and Google testimonies for the Senate and House Intelligence Committees confirmed that a religiously divisive Texas protest was organized by Russian cyber actors. With the intent to sow division and instigate real-world conflict, the actors organized the event and encouraged protestors on both sides of the topic to participate. US competitors in critical Russian spaces or others proximal to the region should incorporate these threat scenarios in their incident response planning.
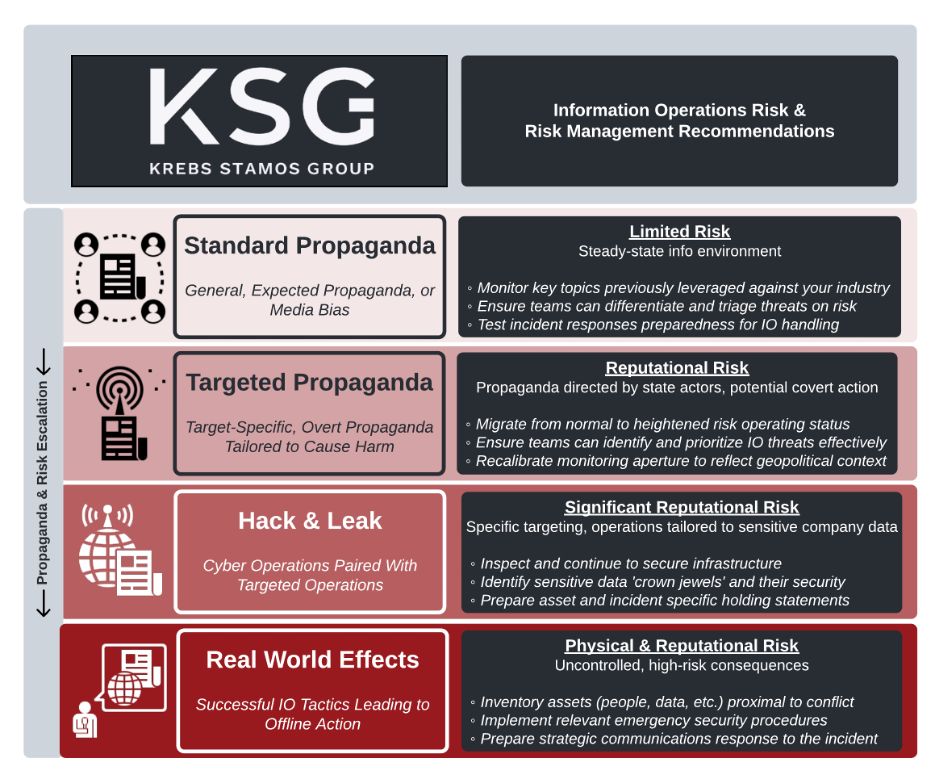
Summary graphic of types of information operations, their potential risks to businesses, and recommended course of actions.
Shields Up: Building Resilience and Preparing Response
A large, public company requires executive-level coordination to understand the risks posed by these information operations and prepare an effective response. KSG recommends the following actions that these companies can take immediately to prepare:
Monitor USG and other authoritative sources that may further expose Russian state-backed cyber actor objectives and emerging narratives.
Identify what channels (e.g., social media, traditional media, official statements) and narratives pose the greatest risk for your business, brand, and corporate objectives.
Identify the teams and processes in your organization responsible for identification, escalation, and response to potential threats.
Repurpose existing social media analytics tooling toward monitoring for high-risk narratives, given your organization’s place amidst escalating tensions.
Collaborate with industry leaders and peers to share signals of new narratives which may impact industry or indicate further escalatory action in the region.
Establish partnerships with researchers, academics, and think-tanks involved in tracking state-backed propaganda and online disinformation campaigns (e.g., DFRLab, U.S. Global Engagement Center, etc.)
As appropriate, exchange tips and leads with relevant points of contact in government departments and agencies dealing with state-backed online manipulation (e.g., FBI Foreign Influence Task Force, UK National Cyber Security Centre).
Prepare holding statements as appropriate to enable situational awareness and ensure public statements aligned with organizational policies are in place.